A hybrid deployment is a combination of On-premises Server and and Cloud-based services. The Hybrid Configuration Wizard actually helps you achieve this. You get the seamless look and feel of a single Exchange organization between an On-Premises Exchange organization and Exchange Online in Microsoft Office 365.
Hybrid Configuration Wizard enables the MRS proxy which is required to migrate mailboxes from and to Office 365.
HCW creates the Hybrid Configuration object in your on-premises Active Directory which stores the hybrid configuration information for the hybrid deployment and is updated by the Hybrid Configuration wizard.
Deploying a Hybrid Environment is one of the most complicated tasks during Migration to Office 365. Sometimes it takes weeks to collect data about infrastructure, designing the plan in stages. Even taking every precaution there is no guarantee that everything will turn out fine. I myself have been into situations many times where one single missed out step failed the HCW.
Hence, I would like to share a Step by Step Guide to perform Hybrid Configuration Wizard (HCW):
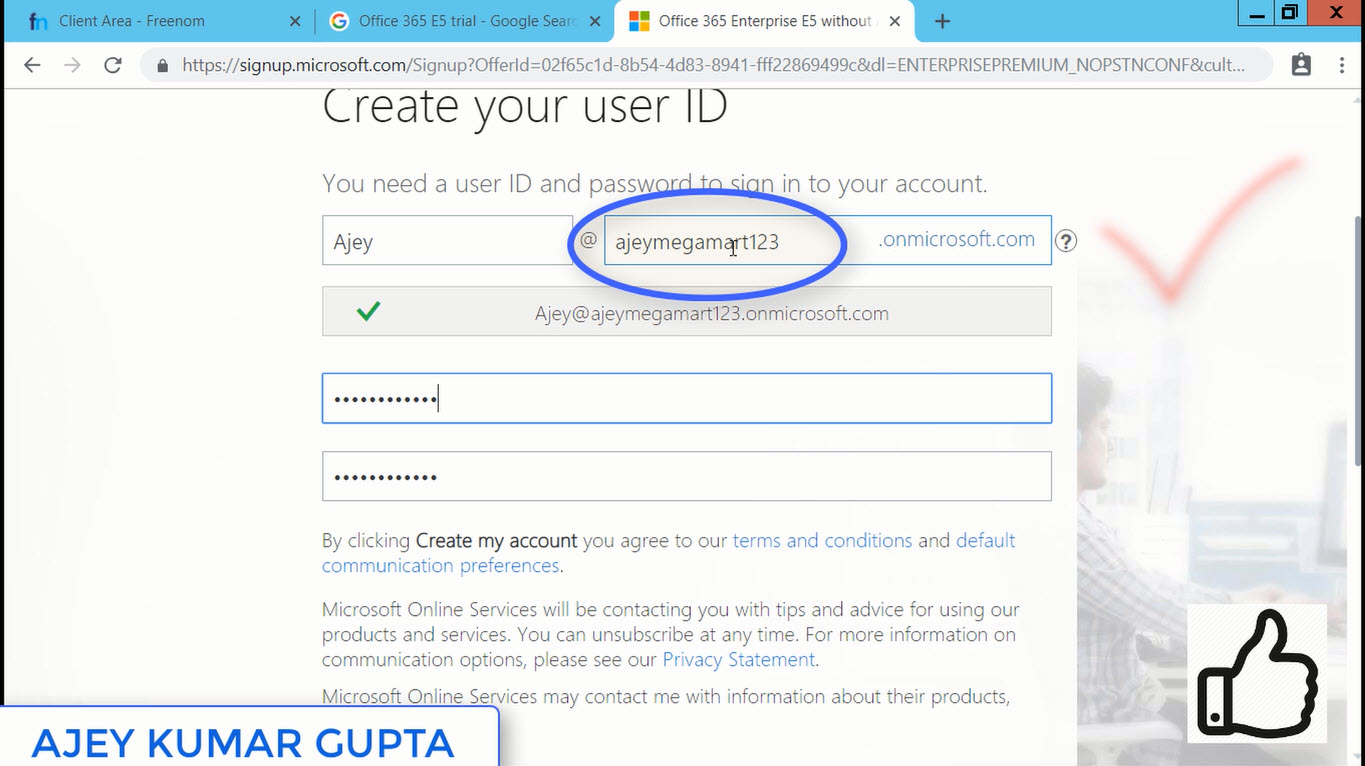
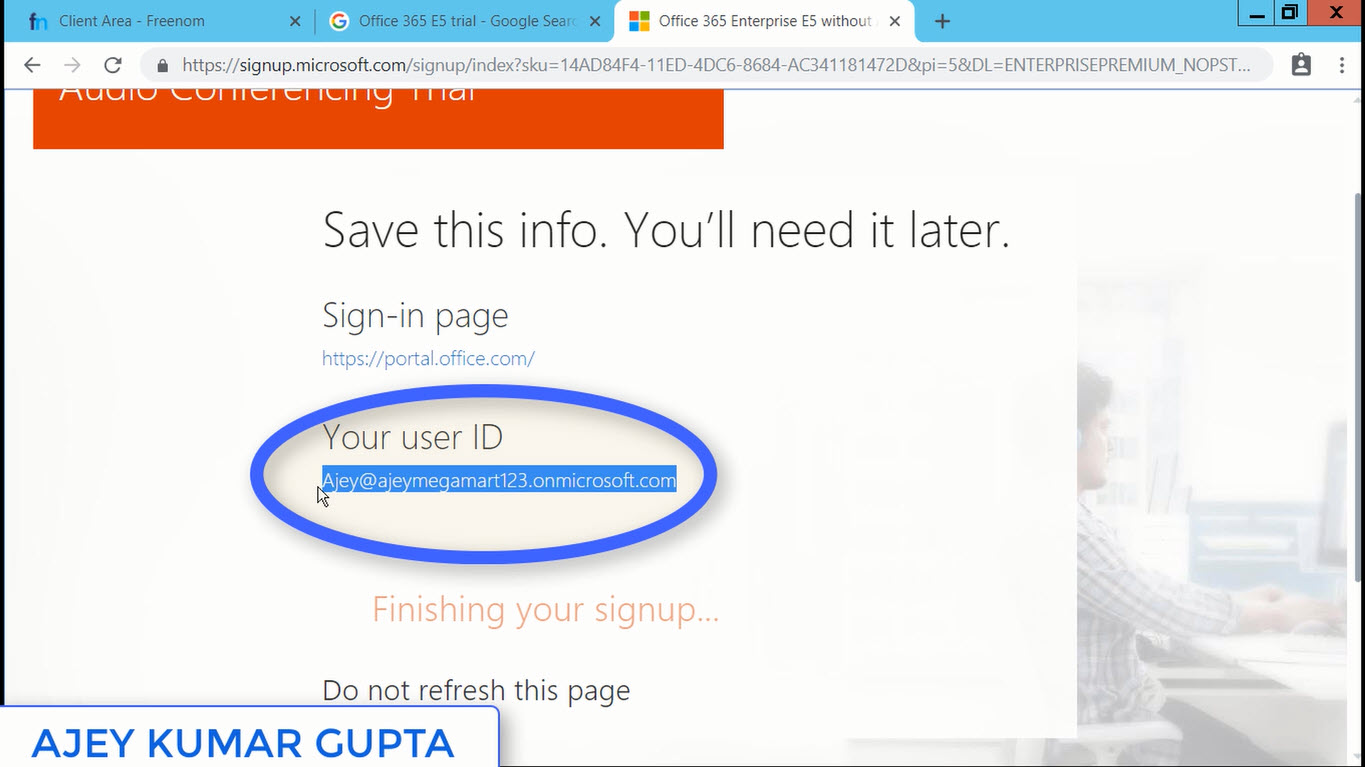
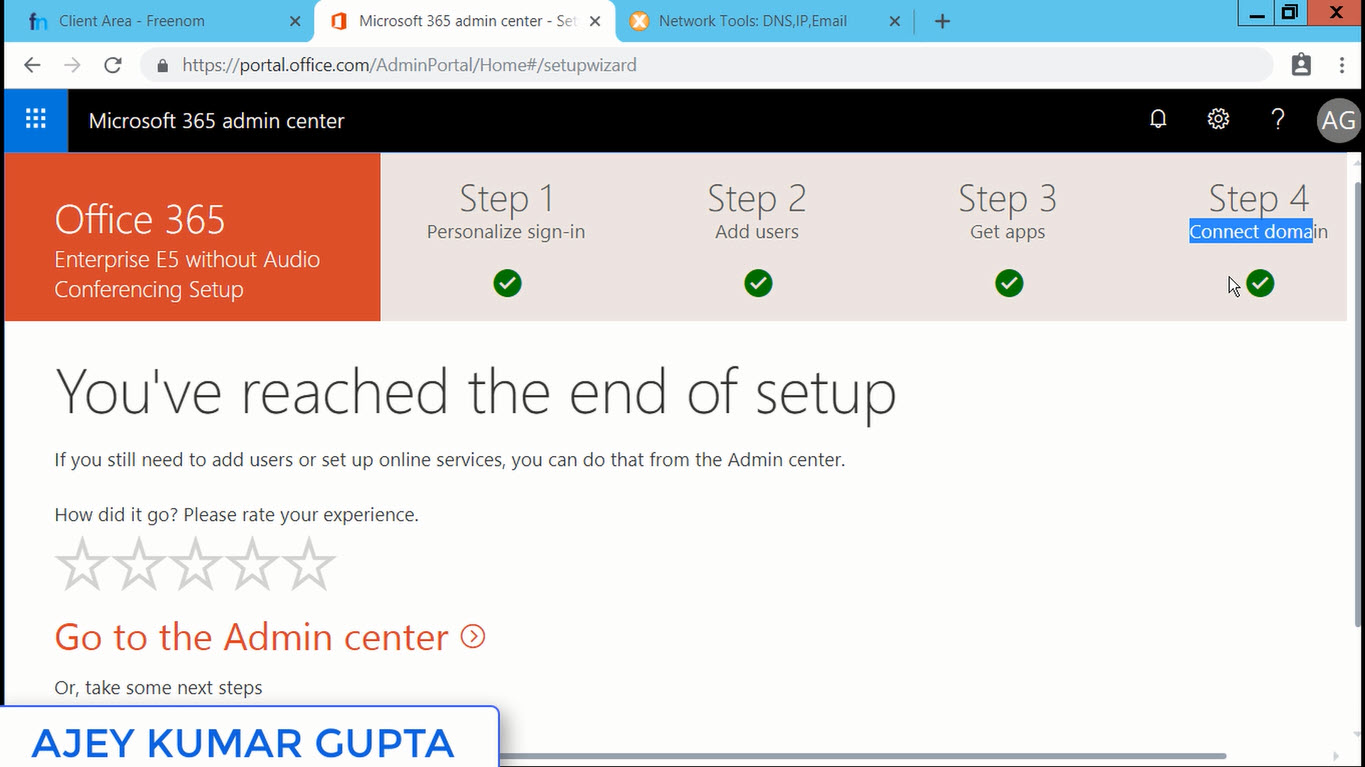
Step 1: Open Internet Explorer - Login into portal.office.com with Global Administrator - Exchange Admin Center - At Left Bottom corner click Hybrid - Click Configure which will download a file - Run it. (Note: Don't use Google Chrome, use Internet Explorer)
Step 2: Once you run the setup, it creates a shortcut on Desktop, and the configuration window will open Automatically - click Next.
At this step HCW searches the right Exchange Server in your Organization. It will point to the CAS Server. Click Next.
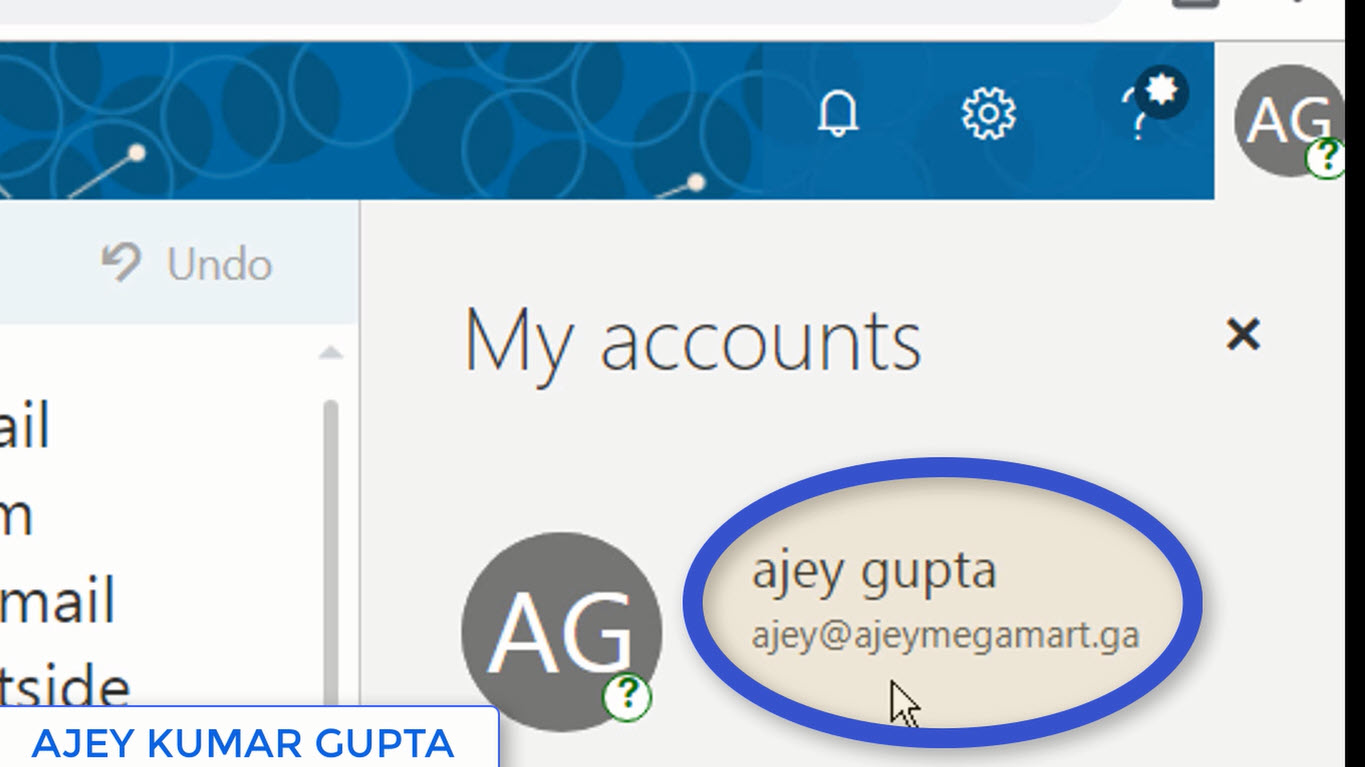
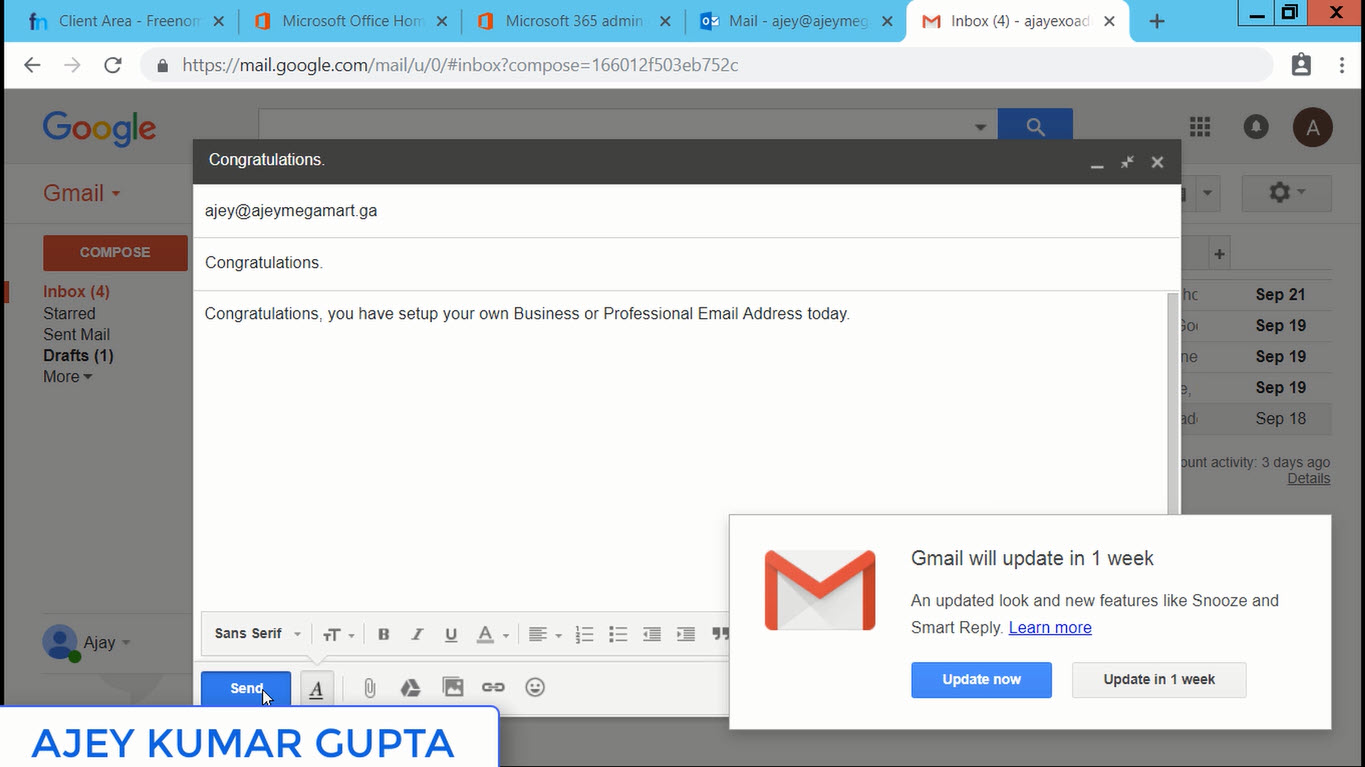
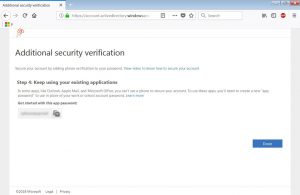
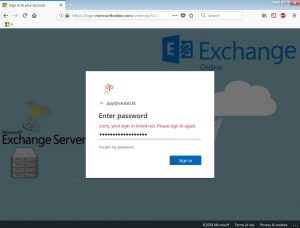
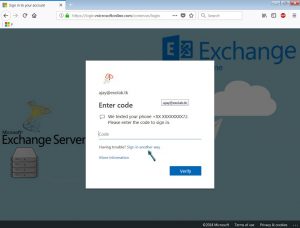
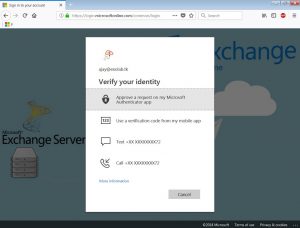
Step 3: Enter your On-premise Exchange Server Administrator Credentials and the Office 365 Global Administrator Credentials. HCW tries to login into each server using Powershell.
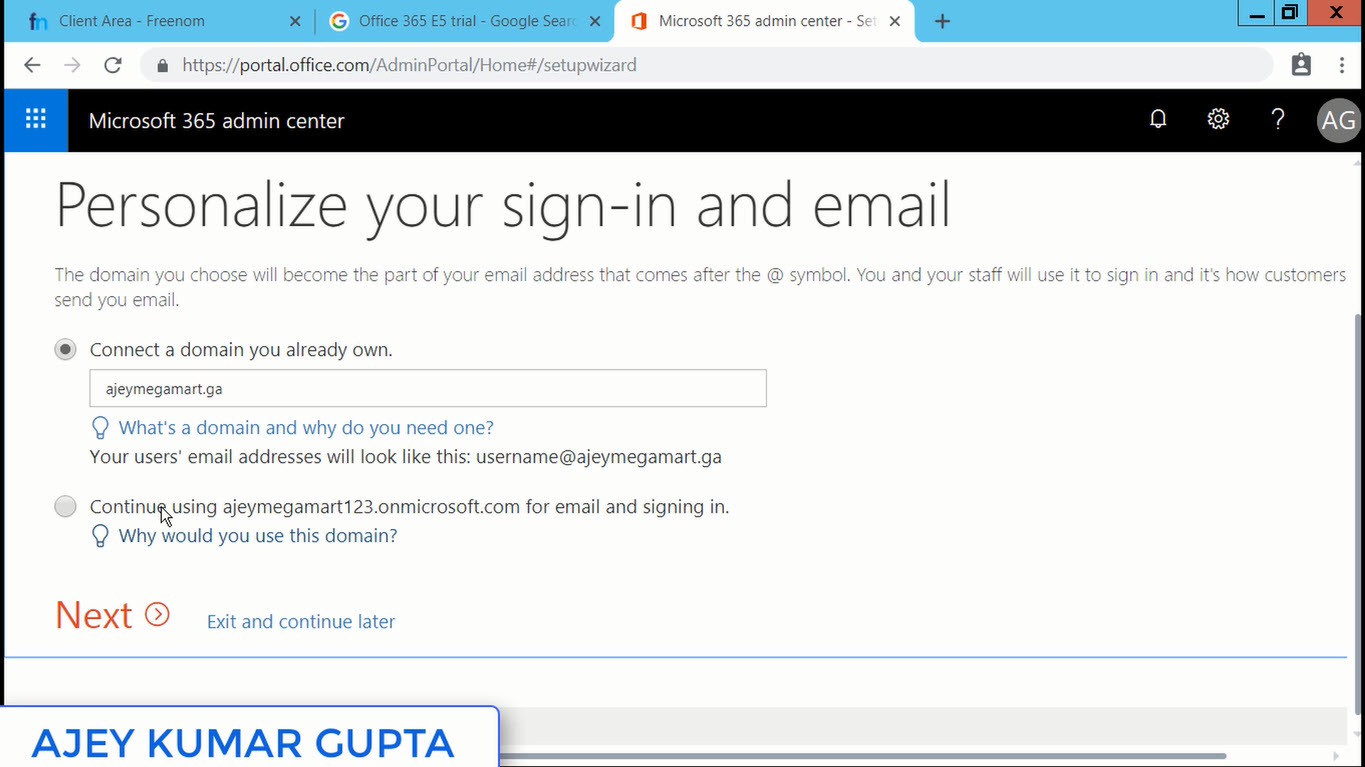
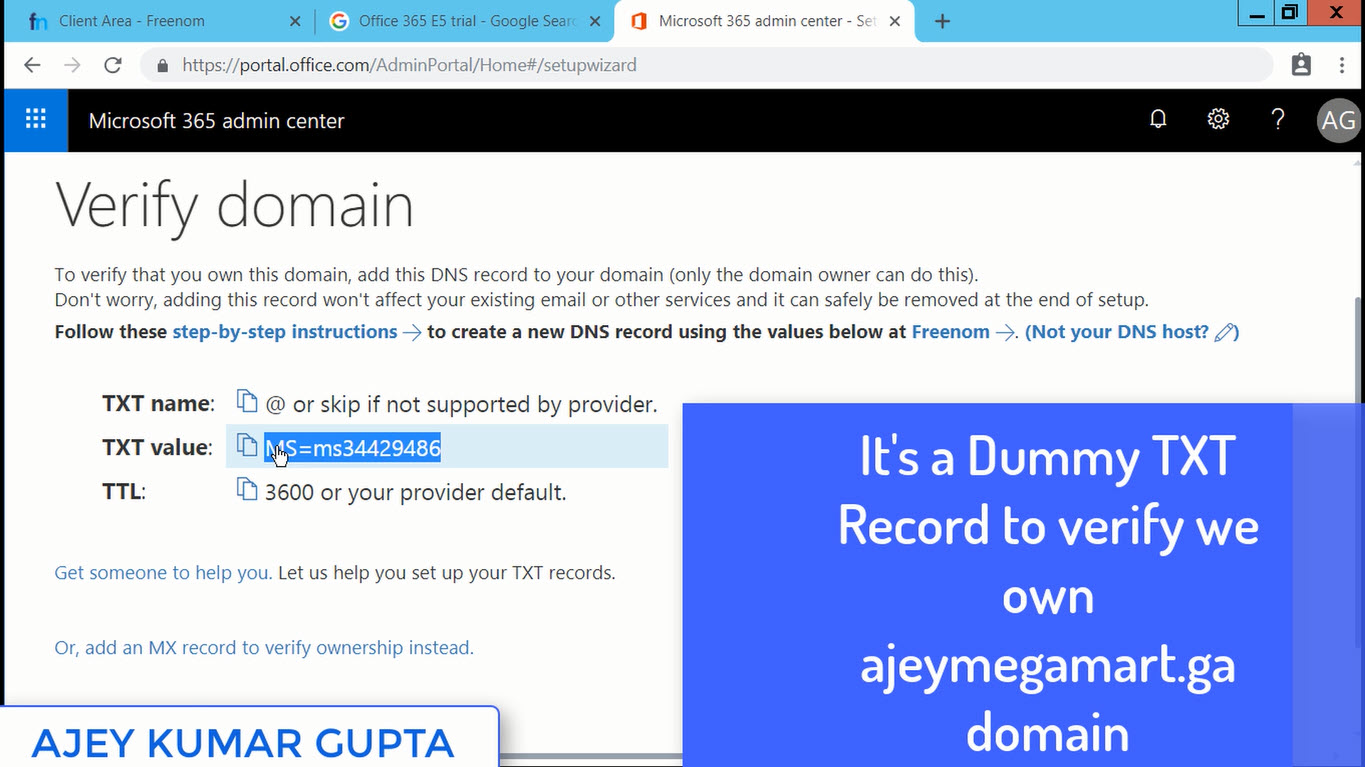
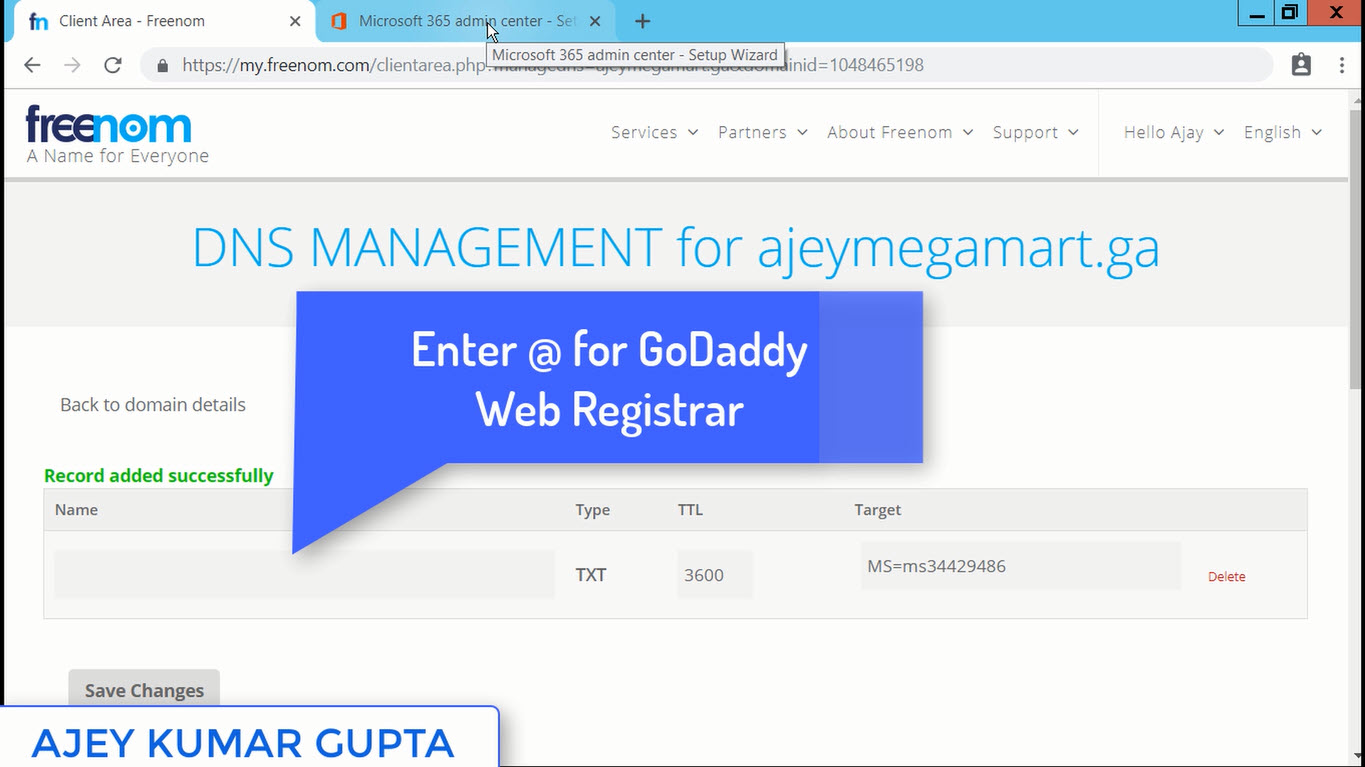
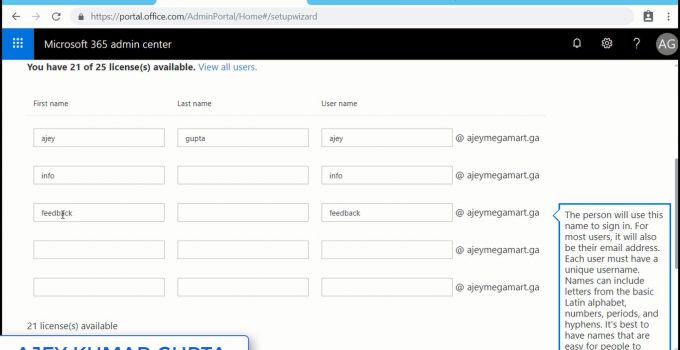
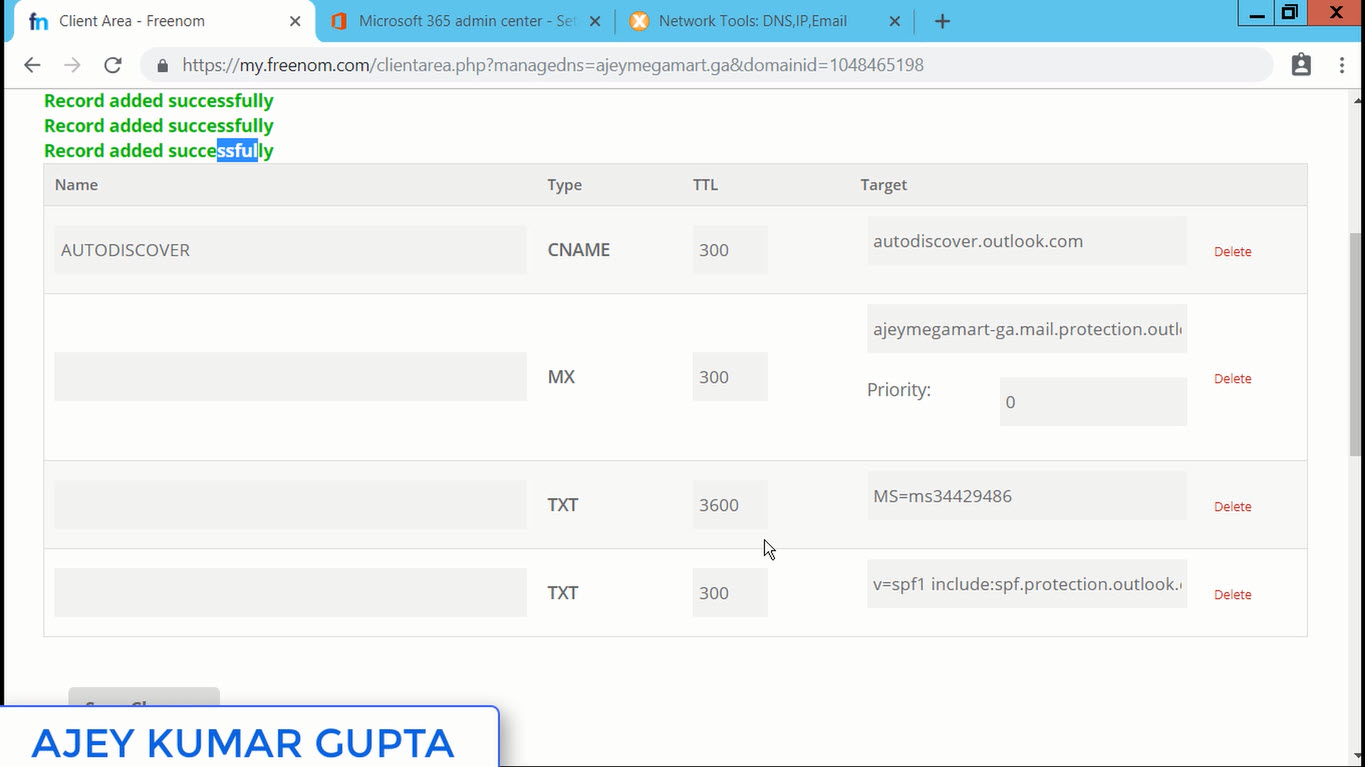
Step 4: Next Steps if Setting Up Federation Trust. Its required for full Hybrid deployment. It enables sharing calendar free/busy information. It will list the domains and you have to prove that you own that. For that a TXT Record you have to add in your Domain DNS Registrar.
Step 5: HCW will ask you to provide the Transport Certificate (3rd Party CA) which will be used to secured Email Flow between On-Premise & Office 365 Tenant.
Step 6: Enter your Public Ip Address. You can use FQDN of the On-Premise Server as well, however it should resolve to your Public Ip address provided by your ISP. The ports 25 (EWS) and 443 (OWA) should be open. Click Next.
Step 7: HCW will start the Configuration Process and will enable your On-premise Exchange Server and Office 365 Tenant into a single Hybrid Organization.
Step 8: Finally if everything went well, you will receive the message Congratulations, Hybrid Services are now configured.......
Friends wasn't that easy? It was :) I have included a Video Presentation just for you:
Now after completing it, most of the Exchange Admins wonder what would have got changed in their infrastructure and how to find that everything is fine.
Look for the logs at the location for any issue:
Location of the Log File:
%AppData%RoamingMicrosoftExchange Hybrid Configuration
Look for the .txt file and search:
Activity=OnPremises Connection Validation
Activity=Tenant Connection Validation
You can check the Hybrid Configuration using Exchange Management Shell: Get-HybridConfiguration
Changes seen at On-Premise Exchange Server:
a) EMailAddressPolicy - an addition with one smtp address "@tenant.mail.onmicrosoft.com"
b) Remote Domain - an addition with tenant.mail.onmicrosoft.com and tenant.onmicrosoft.com
c) Accepted Domain - an addition with tenant.mail.onmicrosoft.com
You can also check the above changes using Exchange Management Shell:
a) EMailAddressPolicy
Get-EmailAddressPolicy | FL Name,EnabledEmailAddressTemplates
b) Remote Domain
Get-RemoteDomain
c) Accepted Domain
Get-AcceptedDomain
To view all data about the Organization Relationship, use your Power Shell console: Get-OrganizationRelationship
Even it looks simple, HCW performs major complicated tasks at the backend for us and we have covered them mostly.
I hope you would have understood how easy it is to setup Hybrid Configuration Wizard. If you find this useful, do let me know by leaving your comment below.
Read More: Click Here
Ajey Kumar Gupta
(Microsoft Exchange Admin)
Next Blog: Google AdSense के अंदर की Terms को समझें | CPC, RPM, AD Units, Monetization etc.
Hybrid Configuration Wizard enables the MRS proxy which is required to migrate mailboxes from and to Office 365.
HCW creates the Hybrid Configuration object in your on-premises Active Directory which stores the hybrid configuration information for the hybrid deployment and is updated by the Hybrid Configuration wizard.
Deploying a Hybrid Environment is one of the most complicated tasks during Migration to Office 365. Sometimes it takes weeks to collect data about infrastructure, designing the plan in stages. Even taking every precaution there is no guarantee that everything will turn out fine. I myself have been into situations many times where one single missed out step failed the HCW.
Hence, I would like to share a Step by Step Guide to perform Hybrid Configuration Wizard (HCW):
Step 1: Open Internet Explorer - Login into portal.office.com with Global Administrator - Exchange Admin Center - At Left Bottom corner click Hybrid - Click Configure which will download a file - Run it. (Note: Don't use Google Chrome, use Internet Explorer)
Step 2: Once you run the setup, it creates a shortcut on Desktop, and the configuration window will open Automatically - click Next.
At this step HCW searches the right Exchange Server in your Organization. It will point to the CAS Server. Click Next.
Step 3: Enter your On-premise Exchange Server Administrator Credentials and the Office 365 Global Administrator Credentials. HCW tries to login into each server using Powershell.
Step 4: Next Steps if Setting Up Federation Trust. Its required for full Hybrid deployment. It enables sharing calendar free/busy information. It will list the domains and you have to prove that you own that. For that a TXT Record you have to add in your Domain DNS Registrar.
Step 5: HCW will ask you to provide the Transport Certificate (3rd Party CA) which will be used to secured Email Flow between On-Premise & Office 365 Tenant.
Step 6: Enter your Public Ip Address. You can use FQDN of the On-Premise Server as well, however it should resolve to your Public Ip address provided by your ISP. The ports 25 (EWS) and 443 (OWA) should be open. Click Next.
Step 7: HCW will start the Configuration Process and will enable your On-premise Exchange Server and Office 365 Tenant into a single Hybrid Organization.
Step 8: Finally if everything went well, you will receive the message Congratulations, Hybrid Services are now configured.......
Friends wasn't that easy? It was :) I have included a Video Presentation just for you:
Look for the logs at the location for any issue:
Location of the Log File:
%AppData%RoamingMicrosoftExchange Hybrid Configuration
Look for the .txt file and search:
Activity=OnPremises Connection Validation
Activity=Tenant Connection Validation
You can check the Hybrid Configuration using Exchange Management Shell: Get-HybridConfiguration
Changes seen at On-Premise Exchange Server:
a) EMailAddressPolicy - an addition with one smtp address "@tenant.mail.onmicrosoft.com"
b) Remote Domain - an addition with tenant.mail.onmicrosoft.com and tenant.onmicrosoft.com
c) Accepted Domain - an addition with tenant.mail.onmicrosoft.com
You can also check the above changes using Exchange Management Shell:
a) EMailAddressPolicy
Get-EmailAddressPolicy | FL Name,EnabledEmailAddressTemplates
b) Remote Domain
Get-RemoteDomain
c) Accepted Domain
Get-AcceptedDomain
To view all data about the Organization Relationship, use your Power Shell console: Get-OrganizationRelationship
Even it looks simple, HCW performs major complicated tasks at the backend for us and we have covered them mostly.
I hope you would have understood how easy it is to setup Hybrid Configuration Wizard. If you find this useful, do let me know by leaving your comment below.
Read More: Click Here
Ajey Kumar Gupta
(Microsoft Exchange Admin)
Next Blog: Google AdSense के अंदर की Terms को समझें | CPC, RPM, AD Units, Monetization etc.